Cause all that matters here is passing the CheckPoint 156-215.81 exam. Cause all that you need is a high score of 156-215.81 Check Point Certified Security Administrator R81 exam. The only one thing you need to do is downloading Actualtests 156-215.81 exam study guides now. We will not let you down with our money-back guarantee.
Online 156-215.81 free questions and answers of New Version:
NEW QUESTION 1
How many users can have read/write access in Gaia Operating System at one time?
- A. One
- B. Three
- C. Two
- D. Infinite
Answer: A
Explanation:
if another user has r/w access, you need to use "lock database override" or "unlock database" to claim r/w access. Ref: https://sc1.checkpoint.com/documents/R80.20_GA/WebAdminGuides/EN/CP_R80.20_Gaia_AdminGuide/html
NEW QUESTION 2
Which of the following is NOT an option to calculate the traffic direction?
- A. Incoming
- B. Internal
- C. External
- D. Outgoing
Answer: D
NEW QUESTION 3
Which Threat Prevention profile uses sanitization technology?
- A. Cloud/data Center
- B. perimeter
- C. Sandbox
- D. Guest Network
Answer: B
Explanation:
Strict Security for Perimeter Profile & Perimeter Profile use sanitization as a technology in Threat prevention profile
NEW QUESTION 4
Fill in the blank: An identity server uses a _____ for user authentication.
- A. Shared secret
- B. Certificate
- C. One-time password
- D. Token
Answer: A
NEW QUESTION 5
You are the Check Point administrator for Alpha Corp. You received a call that one of the users is unable to browse the Internet on their new tablet which is connected to the company wireless, which goes through a Check Point Gateway. How would you review the logs to see what is blocking this traffic?
- A. Open SmartLog and connect remotely to the wireless controller
- B. Open SmartEvent to see why they are being blocked
- C. Open SmartDashboard and review the logs tab
- D. From SmartConsole, go to the Log & Monitor and filter for the IP address of the tablet.
Answer: D
NEW QUESTION 6
True or False: In R80, more than one administrator can login to the Security Management Server with write permission at the same time.
- A. False, this feature has to be enabled in the Global Properties.
- B. True, every administrator works in a session that is independent of the other administrators.
- C. True, every administrator works on a different database that is independent of the other administrators.
- D. False, only one administrator can login with write permission.
Answer: B
Explanation:
More than one administrator can connect to the Security Management Server at the same time. Every administrator has their own username, and works in a session that is independent of the other administrators.
NEW QUESTION 7
You are going to perform a major upgrade. Which back up solution should you use to ensure your database can be restored on that device?
- A. backup
- B. logswitch
- C. Database Revision
- D. snapshot
Answer: D
Explanation:
The snapshot creates a binary image of the entire root (lv_current) disk partition. This includes Check Point products, configuration, and operating system.
Starting in R77.10, exporting an image from one machine and importing that image on another machine of the same type is supported.
The log partition is not included in the snapshot. Therefore, any locally stored FireWall logs will not be save
NEW QUESTION 8
Which of the following commands is used to monitor cluster members?
- A. cphaprob state
- B. cphaprob status
- C. cphaprob
- D. cluster state
Answer: A
NEW QUESTION 9
CPU-level of your Security gateway is peaking to 100% causing problems with traffic. You suspect that the problem might be the Threat Prevention settings.
The following Threat Prevention Profile has been created.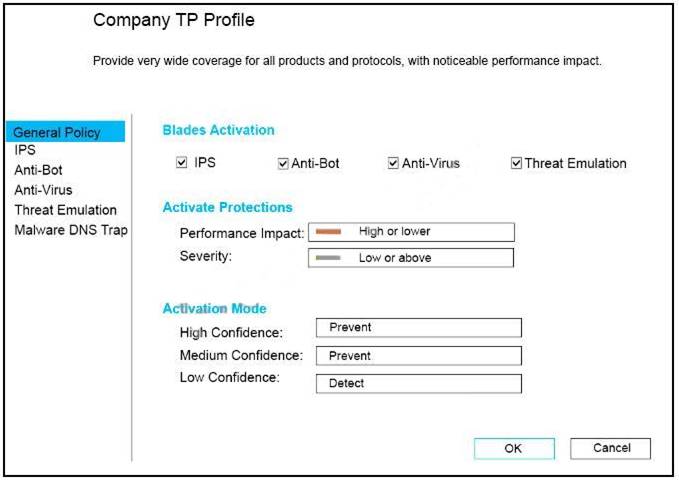
How could you tune the profile in order to lower the CPU load still maintaining security at good level? Select the BEST answer.
- A. Set High Confidence to Low and Low Confidence to Inactive.
- B. Set the Performance Impact to Medium or lower.
- C. The problem is not with the Threat Prevention Profil
- D. Consider adding more memory to the appliance.
- E. Set the Performance Impact to Very Low Confidence to Prevent.
Answer: B
NEW QUESTION 10
How would you determine the software version from the CLI?
- A. fw ver
- B. fw stat
- C. fw monitor
- D. cpinfo
Answer: A
NEW QUESTION 11
Which default Gaia user has full read/write access?
- A. admin
- B. superuser
- C. monitor
- D. altuser
Answer: A
Explanation:
Has full read/write capabilities for all Gaia features, from the Gaia Portal and the Gaia Clish. This user has a User ID of 0, and therefore has all of the privileges of a root user. monitor Has read-only capabilities for all features in the Gaia Portal and the Gaia Clish, and can change its own password. You must give a password for this user before the account can be used.
NEW QUESTION 12
Fill in the blanks: Gaia can be configured using _______ the ________.
- A. Command line interface; WebUI
- B. Gaia Interface; GaiaUI
- C. WebUI; Gaia Interface
- D. GaiaUI; command line interface
Answer: A
Explanation:
https://sc1.checkpoint.com/documents/R81/WebAdminGuides/EN/CP_R81_Gaia_AdminGuide/Topics-GAG/C
NEW QUESTION 13
Which method below is NOT one of the ways to communicate using the Management API’s?
- A. Typing API commands using the “mgmt_cli” command
- B. Typing API commands from a dialog box inside the SmartConsole GUI application
- C. Typing API commands using Gaia’s secure shell (clash)19+
- D. Sending API commands over an http connection using web-services
Answer: D
NEW QUESTION 14
Fill in the blanks: In _______ NAT, Only the _______ is translated.
- A. Static; source
- B. Simple; source
- C. Hide; destination
- D. Hide; source
Answer: D
Explanation:
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=
NEW QUESTION 15
Check Point licenses come in two forms. What are those forms?
- A. Central and Local.
- B. Access Control and Threat Prevention.
- C. On-premise and Public Cloud.
- D. Security Gateway and Security Management.
Answer: A
NEW QUESTION 16
......
100% Valid and Newest Version 156-215.81 Questions & Answers shared by Surepassexam, Get Full Dumps HERE: https://www.surepassexam.com/156-215.81-exam-dumps.html (New 400 Q&As)
