Act now and download your Cisco 350-701 test today! Do not waste time for the worthless Cisco 350-701 tutorials. Download Avant-garde Cisco Implementing and Operating Cisco Security Core Technologies exam with real questions and answers and begin to learn Cisco 350-701 with a classic professional.
Cisco 350-701 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which technology reduces data loss by identifying sensitive information stored in public computing environments?
- A. Cisco SDA
- B. Cisco Firepower
- C. Cisco HyperFlex
- D. Cisco Cloudlock
Answer: D
NEW QUESTION 2
An organization must add new firewalls to its infrastructure and wants to use Cisco ASA or Cisco FTD.
The chosen firewalls must provide methods of blocking traffic that include offering the user the option to bypass the block for certain sites after displaying a warning page and to reset the connection. Which solution should the organization choose?
- A. Cisco FTD because it supports system rate level traffic blocking, whereas Cisco ASA does not
- B. Cisco ASA because it allows for interactive blocking and blocking with reset to be configured via the GUI, whereas Cisco FTD does not.
- C. Cisco FTD because it enables interactive blocking and blocking with reset natively, whereas Cisco ASAdoes not
- D. Cisco ASA because it has an additional module that can be installed to provide multiple blocking capabilities, whereas Cisco FTD does not.
Answer: C
NEW QUESTION 3
Which kind of API that is used with Cisco DNA Center provisions SSIDs, QoS policies, and update software versions on switches?
- A. Integration
- B. Intent
- C. Event
- D. Multivendor
Answer: B
NEW QUESTION 4
Which option is the main function of Cisco Firepower impact flags?
- A. They alert administrators when critical events occur.
- B. They highlight known and suspected malicious IP addresses in reports.
- C. They correlate data about intrusions and vulnerability.
- D. They identify data that the ASA sends to the Firepower module.
Answer: C
NEW QUESTION 5
Which method of attack is used by a hacker to send malicious code through a web application to an unsuspecting user to request that the victim's web browser executes the code?
- A. buffer overflow
- B. browser WGET
- C. SQL injection
- D. cross-site scripting
Answer: D
NEW QUESTION 6
What provides visibility and awareness into what is currently occurring on the network?
- A. CMX
- B. WMI
- C. Prime Infrastructure
- D. Telemetry
Answer: D
Explanation:
Reference: https://www.cisco.com/c/dam/en_us/about/doing_business/legal/service_descriptions/docs/activethreat-analytics
NEW QUESTION 7
An organization wants to secure users, data, and applications in the cloud. The solution must be API-based and operate as a cloud-native CASB. Which solution must be used for this implementation?
- A. Cisco Cloudlock
- B. Cisco Cloud Email Security
- C. Cisco Firepower Next-Generation Firewall
- D. Cisco Umbrella
Answer: A
Explanation:
Reference:
https://www.cisco.com/c/dam/en/us/products/collateral/security/cloud-web-security/at-a-glance-c45-738565.pdf
NEW QUESTION 8
Which Cisco security solution protects remote users against phishing attacks when they are not connected to the VPN?
- A. Cisco Stealthwatch
- B. Cisco Umbrella
- C. Cisco Firepower
- D. NGIPS
Answer: B
Explanation:
Cisco Umbrella protects users from accessing malicious domains by proactively analyzing and blocking unsafe destinations – before a connection is ever made. Thus it can protect from phishing attacks by blocking suspicious domains when users click on the given links that an attacker sent. Cisco Umbrella roaming protects your employees even when they are off the VPN.
NEW QUESTION 9
Refer to the exhibit.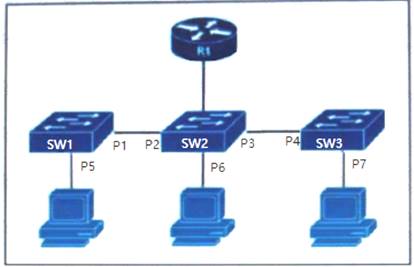
The DHCP snooping database resides on router R1, and dynamic ARP inspection is configured only on switch SW2. Which ports must be configured as untrusted so that dynamic ARP inspection operates normally?
- A. P2 and P3 only
- B. P5, P6, and P7 only
- C. P1, P2, P3, and P4 only
- D. P2, P3, and P6 only
Answer: D
NEW QUESTION 10
Which DevSecOps implementation process gives a weekly or daily update instead of monthly or quarterly in the applications?
- A. Orchestration
- B. CI/CD pipeline
- C. Container
- D. Security
Answer: B
Explanation:
Reference: https://devops.com/how-to-implement-an-effective-ci-cd-pipeline/
NEW QUESTION 11
An engineer has been tasked with configuring a Cisco FTD to analyze protocol fields and detect anomalies in the traffic from industrial systems. What must be done to meet these requirements?
- A. Implement pre-filter policies for the CIP preprocessor
- B. Enable traffic analysis in the Cisco FTD
- C. Configure intrusion rules for the DNP3 preprocessor
- D. Modify the access control policy to trust the industrial traffic
Answer: C
Explanation:
"configure INTRUSION RULES for DNP3" -> Documentation states, that enabling INTRUSION RULES is mandatory for CIP to work + required preprocessors (in Network Access Policy - NAP) will be enabled automatically:
"If you want the CIP preprocessor rules listed in the following table to generate events, you MUST enable them. See Setting Intrusion Rule States for information on enabling rules."
"If the Modbus, DNP3, or CIP preprocessor is disabled, and you enable and deploy an intrusion rule that requires one of these preprocessors, the system automatically uses the required preprocessor, with its current settings, although the preprocessor remains disabled in the web interface for the corresponding network analysis policy."
[1]
https://www.cisco.com/c/en/us/td/docs/security/firepower/630/configuration/guide/fpmc-config-guide-v63/scada
NEW QUESTION 12
Which Cisco DNA Center Intent API action is used to retrieve the number of devices known to a DNA Center?
- A. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v1/network-device/count
- B. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v1/network-device
- C. GEThttps://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v1/networkdevice?parameter1=value¶meter2=v
- D. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v 1/networkdevice/startIndex/recordsToReturn
Answer: A
NEW QUESTION 13
What does the Cloudlock Apps Firewall do to mitigate security concerns from an application perspective?
- A. It allows the administrator to quarantine malicious files so that the application can function, just not maliciously.
- B. It discovers and controls cloud apps that are connected to a company’s corporate environment.
- C. It deletes any application that does not belong in the network.
- D. It sends the application information to an administrator to act on.
Answer: B
NEW QUESTION 14
Refer to the exhibit.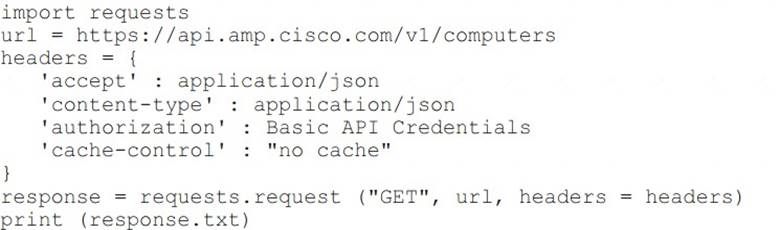
What will happen when this Python script is run?
- A. The compromised computers and malware trajectories will be received from Cisco AMP
- B. The list of computers and their current vulnerabilities will be received from Cisco AMP
- C. The compromised computers and what compromised them will be received from Cisco AMP
- D. The list of computers, policies, and connector statuses will be received from Cisco AMP
Answer: D
Explanation:
Reference:
https://api-docs.amp.cisco.com/api_actions/details?api_action=GET+%2Fv1%2Fcomputers&api_host=api.apjc.
NEW QUESTION 15
A company discovered an attack propagating through their network via a file. A custom file policy was created in order to track this in the future and ensure no other endpoints execute the infected file. In addition, it was discovered during testing that the scans are not detecting the file as an indicator of compromise. What must be done in order to ensure that the created is functioning as it should?
- A. Create an IP block list for the website from which the file was downloaded
- B. Block the application that the file was using to open
- C. Upload the hash for the file into the policy
- D. Send the file to Cisco Threat Grid for dynamic analysis
Answer: C
NEW QUESTION 16
How does a WCCP-configured router identify if the Cisco WSA is functional?
- A. If an ICMP ping fails three consecutive times between a router and the WSA, traffic is no longer transmitted to the router.
- B. If an ICMP ping fails three consecutive times between a router and the WSA, traffic is no longer transmitted to the WSA.
- C. The WSA sends a Here-l-Am message every 10 seconds, and the router acknowledges with an ISee-You message.
- D. The router sends a Here-l-Am message every 10 seconds, and the WSA acknowledges with an ISee-You message.
Answer: C
NEW QUESTION 17
Which security solution is used for posture assessment of the endpoints in a BYOD solution?
- A. Cisco FTD
- B. Cisco ASA
- C. Cisco Umbrella
- D. Cisco ISE
Answer: D
NEW QUESTION 18
What does Cisco AMP for Endpoints use to help an organization detect different families of malware?
- A. Ethos Engine to perform fuzzy fingerprinting
- B. Tetra Engine to detect malware when me endpoint is connected to the cloud
- C. Clam AV Engine to perform email scanning
- D. Spero Engine with machine learning to perform dynamic analysis
Answer: A
Explanation:
Reference: https://docs.amp.cisco.com/AMP%20for%20Endpoints%20User%20Guide.pdfETHOS = Fuzzy Fingerprinting using static/passive heuristics
Reference: https://www.ciscolive.com/c/dam/r/ciscolive/emea/docs/2016/pdf/BRKSEC-2139.pdf
NEW QUESTION 19
A network engineer has entered the snmp-server user andy myv3 auth sha cisco priv aes 256 cisc0380739941 command and needs to send SNMP information to a host at 10.255.254.1. Which command achieves this goal?
- A. snmp-server host inside 10.255.254.1 version 3 andy
- B. snmp-server host inside 10.255.254.1 version 3 myv3
- C. snmp-server host inside 10.255.254.1 snmpv3 andy
- D. snmp-server host inside 10.255.254.1 snmpv3 myv3
Answer: A
Explanation:
The command “snmp-server user user-name group-name [remote ip-address [udp-port port]]
{v1 | v2c | v3 [encrypted] [auth {md5 | sha} auth-password]} [access access-list]” adds a new user (in this case “andy”) to an SNMPv3 group (in this case group name “myv3”) and configures a password for the user.In the “snmp-server host” command, we need to:+ Specify the SNMP version with key word “version {1 | 2 | 3}”+ Specify the username (“andy”), not group name (“myv3”).Note: In “snmp-server host inside …” command, “inside” is the interface name of the ASA interface through which the NMS (located at 10.255.254.1) can be reached.
NEW QUESTION 20
......
100% Valid and Newest Version 350-701 Questions & Answers shared by Downloadfreepdf.net, Get Full Dumps HERE: https://www.downloadfreepdf.net/350-701-pdf-download.html (New 631 Q&As)
