Approved of 350-701 training materials and vce for Cisco certification for consumer, Real Success Guaranteed with Updated 350-701 pdf dumps vce Materials. 100% PASS Implementing and Operating Cisco Security Core Technologies exam Today!
Cisco 350-701 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which feature of Cisco ASA allows VPN users to be postured against Cisco ISE without requiring an inline posture node?
- A. RADIUS Change of Authorization
- B. device tracking
- C. DHCP snooping
- D. VLAN hopping
Answer: A
NEW QUESTION 2
A network administrator is configuring a role in an access control policy to block certain URLs and selects the "Chat and instant Messaging" category. which reputation score should be selected to accomplish
this goal?
- A. 3
- B. 5
- C. 10
- D. 1
Answer: C
NEW QUESTION 3
Which two commands are required when configuring a flow-export action on a Cisco ASA? (Choose two.)
- A. flow-export event-type
- B. policy-map
- C. access-list
- D. flow-export template timeout-rate 15
- E. access-group
Answer: AB
NEW QUESTION 4
When using Cisco AMP for Networks which feature copies a file to the Cisco AMP cloud for analysis?
- A. Spero analysis
- B. dynamic analysis
- C. sandbox analysis
- D. malware analysis
Answer: B
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/security/firepower/60/configuration/guide/fpmc-config-guidev60/Refere Spero analysis only uploads the signature of the (executable) files to the AMP cloud. It does not upload
thewhole file. Dynamic analysis sends files to AMP ThreatGrid.Dynamic Analysis submits (the whole) files to Cisco Threat Grid (formerly AMP Threat Grid). Cisco ThreatGrid runs the file in a sandbox environment, analyzes the file’s behavior to determine whether the file ismalicious, and returns a threat score that indicates the likelihood that a file contains malware. From the threatscore, you can view a dynamic analysis summary report with the reasons for the assigned threat score. Youcan also look in Cisco Threat Grid to view detailed reports for files that your organization submitted, as well asscrubbed reports with limited data for files that your organization did not submit.Local malware analysis allows a managed device to locally inspect executables, PDFs, office documents, andother types of files for the most common types of malware, using a detection rule set provided by the CiscoTalos Security Intelligence and Research Group (Talos). Because local analysis does not query the AMP cloud,and does not run the file, local malware analysis saves time and system resources. -> Malware analysis doesnot upload files to anywhere, it only checks the files locally.There is no sandbox analysis feature, it is just a method of dynamic analysis that runs suspicious files in avirtual machine.
NEW QUESTION 5
Which portion of the network do EPP solutions solely focus on and EDR solutions do not?
- A. server farm
- B. perimeter
- C. core
- D. East-West gateways
Answer: B
NEW QUESTION 6
What are two characteristics of the RESTful architecture used within Cisco DNA Center? (Choose two.)
- A. REST uses methods such as GET, PUT, POST, and DELETE.
- B. REST codes can be compiled with any programming language.
- C. REST is a Linux platform-based architecture.
- D. The POST action replaces existing data at the URL path.
- E. REST uses HTTP to send a request to a web service.
Answer: AE
NEW QUESTION 7
Which two activities can be done using Cisco DNA Center? (Choose two)
- A. DHCP
- B. Design
- C. Accounting
- D. DNS
- E. Provision
Answer: BE
Explanation:
Reference: https://www.cisco.com/c/en/us/products/collateral/cloud-systems-management/dna-center/nb-06-dna-center-so-cte-en.html
NEW QUESTION 8
What are two features of NetFlow flow monitoring? (Choose two)
- A. Can track ingress and egress information
- B. Include the flow record and the flow importer
- C. Copies all ingress flow information to an interface
- D. Does not required packet sampling on interfaces
- E. Can be used to track multicast, MPLS, or bridged traffic
Answer: AE
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/netflow/configuration/15-mt/nf-15-mt-book/cfgmpls-netflow
NEW QUESTION 9
Due to a traffic storm on the network, two interfaces were error-disabled, and both interfaces sent SNMP traps.
Which two actions must be taken to ensure that interfaces are put back into service? (Choose two)
- A. Have Cisco Prime Infrastructure issue an SNMP set command to re-enable the ports after the pre configured interval.
- B. Use EEM to have the ports return to service automatically in less than 300 seconds.
- C. Enter the shutdown and no shutdown commands on the interfaces.
- D. Enable the snmp-server enable traps command and wait 300 seconds
- E. Ensure that interfaces are configured with the error-disable detection and recovery feature
Answer: CE
Explanation:
You can also bring up the port by using these commands:+ The “shutdown” interface configuration command followed by the “no shutdown” interface configurationcommand restarts the disabled port.+ The “errdisable recovery cause …” global configuration command enables the timer to automatically recover error-disabled state, and the “errdisable recovery interval interval” global configuration command specifies the time to recover error-disabled state.
NEW QUESTION 10
What limits communication between applications or containers on the same node?
- A. microsegmentation
- B. container orchestration
- C. microservicing
- D. Software-Defined Access
Answer: D
NEW QUESTION 11
What is the difference between a vulnerability and an exploit?
- A. A vulnerability is a hypothetical event for an attacker to exploit
- B. A vulnerability is a weakness that can be exploited by an attacker
- C. An exploit is a weakness that can cause a vulnerability in the network
- D. An exploit is a hypothetical event that causes a vulnerability in the network
Answer: B
NEW QUESTION 12
Which risk is created when using an Internet browser to access cloud-based service?
- A. misconfiguration of infrastructure, which allows unauthorized access
- B. intermittent connection to the cloud connectors
- C. vulnerabilities within protocol
- D. insecure implementation of API
Answer: D
NEW QUESTION 13
How does Cisco Workload Optimization Manager help mitigate application performance issues?
- A. It deploys an AWS Lambda system
- B. It automates resource resizing
- C. It optimizes a flow path
- D. It sets up a workload forensic score
Answer: B
Explanation:
Reference:
https://www.cisco.com/c/dam/en/us/solutions/collateral/data-center-virtualization/one-enterprisesuite/solution-o
NEW QUESTION 14
Drag and drop the exploits from the left onto the type of security vulnerability on the right.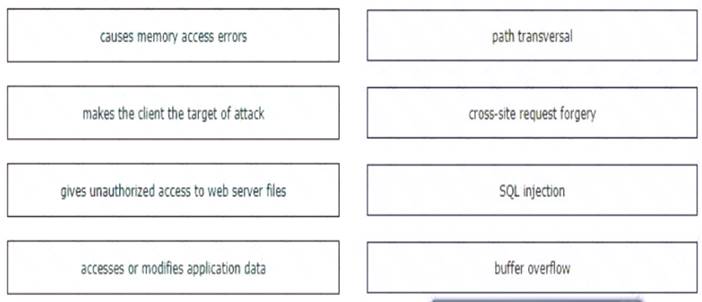
Solution:
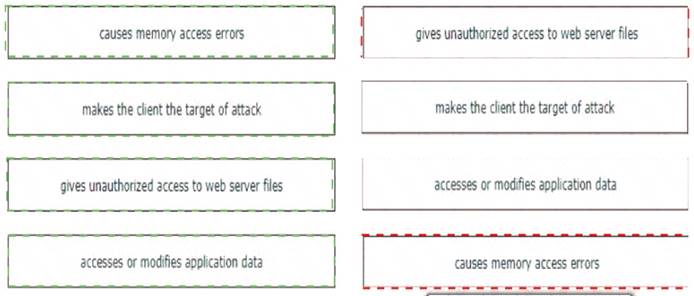
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 15
Which feature must be configured before implementing NetFlow on a router?
- A. SNMPv3
- B. syslog
- C. VRF
- D. IP routing
Answer: D
NEW QUESTION 16
Which benefit is provided by ensuring that an endpoint is compliant with a posture policy configured in Cisco ISE?
- A. It allows the endpoint to authenticate with 802.1x or MAB.
- B. It verifies that the endpoint has the latest Microsoft security patches installed.
- C. It adds endpoints to identity groups dynamically.
- D. It allows CoA to be applied if the endpoint status is compliant.
Answer: A
NEW QUESTION 17
An engineer must modify a policy to block specific addresses using Cisco Umbrella. The policy is created already and is actively u: of the default policy elements. What else must be done to accomplish this task?
- A. Add the specified addresses to the identities list and create a block action.
- B. Create a destination list for addresses to be allowed or blocked.
- C. Use content categories to block or allow specific addresses.
- D. Modify the application settings to allow only applications to connect to required addresses.
Answer: B
NEW QUESTION 18
What is the primary role of the Cisco Email Security Appliance?
- A. Mail Submission Agent
- B. Mail Transfer Agent
- C. Mail Delivery Agent
- D. Mail User Agent
Answer: B
Explanation:
Reference: https://www.cisco.com/c/dam/en/us/td/docs/solutions/SBA/February2013/Cisco_SBA_BN_EmailSecurityUsing
NEW QUESTION 19
An engineer needs to detect and quarantine a file named abc424400664 zip based on the MD5 signature of the file using the Outbreak Control list feature within Cisco Advanced Malware Protection (AMP) for Endpoints The configured detection method must work on files of unknown disposition Which Outbreak Control list must be configured to provide this?
- A. Blocked Application
- B. Simple Custom Detection
- C. Advanced Custom Detection
- D. Android Custom Detection
Answer: C
NEW QUESTION 20
......
P.S. Allfreedumps.com now are offering 100% pass ensure 350-701 dumps! All 350-701 exam questions have been updated with correct answers: https://www.allfreedumps.com/350-701-dumps.html (631 New Questions)
