Proper study guides for Improved Cisco Implementing and Operating Cisco Security Core Technologies certified begins with Cisco 350-701 preparation products which designed to deliver the Download 350-701 questions by making you pass the 350-701 test at your first time. Try the free 350-701 demo right now.
Cisco 350-701 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
Which two prevention techniques are used to mitigate SQL injection attacks? (Choose two)
- A. Check integer, float, or Boolean string parameters to ensure accurate values.
- B. Use prepared statements and parameterized queries.
- C. Secure the connection between the web and the app tier.
- D. Write SQL code instead of using object-relational mapping libraries.
- E. Block SQL code execution in the web application database login.
Answer: AB
NEW QUESTION 2
An engineer needs behavioral analysis to detect malicious activity on the hosts, and is configuring the organization’s public cloud to send telemetry using the cloud provider’s mechanisms to a security device.
Which mechanism should the engineer configure to accomplish this goal?
- A. mirror port
- B. Flow
- C. NetFlow
- D. VPC flow logs
Answer: C
NEW QUESTION 3
What is the role of an endpoint in protecting a user from a phishing attack?
- A. Use Cisco Stealthwatch and Cisco ISE Integration.
- B. Utilize 802.1X network security to ensure unauthorized access to resources.
- C. Use machine learning models to help identify anomalies and determine expected sending behavior.
- D. Ensure that antivirus and anti malware software is up to date
Answer: C
NEW QUESTION 4
What is a commonality between DMVPN and FlexVPN technologies?
- A. FlexVPN and DMVPN use IS-IS routing protocol to communicate with spokes
- B. FlexVPN and DMVPN use the new key management protocol
- C. FlexVPN and DMVPN use the same hashing algorithms
- D. IOS routers run the same NHRP code for DMVPN and FlexVPN
Answer: D
Explanation:
Reference: https://packetpushers.net/cisco-flexvpn-dmvpn-high-level-design/
NEW QUESTION 5
Which feature is leveraged by advanced antimalware capabilities to be an effective endpomt protection platform?
- A. big data
- B. storm centers
- C. sandboxing
- D. blocklisting
Answer: C
NEW QUESTION 6
When planning a VPN deployment, for which reason does an engineer opt for an active/active FlexVPN configuration as opposed to DMVPN?
- A. Multiple routers or VRFs are required.
- B. Traffic is distributed statically by default.
- C. Floating static routes are required.
- D. HSRP is used for faliover.
Answer: B
NEW QUESTION 7
How is DNS tunneling used to exfiltrate data out of a corporate network?
- A. It corrupts DNS servers by replacing the actual IP address with a rogue address to collect information or start other attacks.
- B. It encodes the payload with random characters that are broken into short strings and the DNS server rebuilds the exfiltrated data.
- C. It redirects DNS requests to a malicious server used to steal user credentials, which allows further damageand theft on the network.
- D. It leverages the DNS server by permitting recursive lookups to spread the attack to other DNS servers.
Answer: B
Explanation:
Domain name system (DNS) is the protocol that translates human-friendly URLs, such as securitytut.com, into IP addresses, such as 183.33.24.13. Because DNS messages are only used as the beginning of each communication and they are not intended for data transfer, many organizations do not monitor their DNS traffic for malicious activity. As a result, DNS-based attacks can be effective if launched against their networks. DNS tunneling is one such attack.An example of DNS Tunneling is shown below: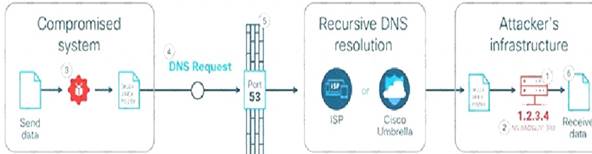
 The attacker incorporates one of many open-source DNS tunneling kits into an authoritative DNSnameserver (NS) and malicious payload.2. An IP address (e.g. 1.2.3.4) is allocated from the attacker’s infrastructure and a domain name (e.g. attackerdomain.com) is registered or reused. The registrar informs the top-level domain (.com) nameservers to refer requests for attackerdomain.com to ns.attackerdomain.com, which has a DNS record mapped to 1.2.3.43. The attacker compromises a system with the malicious payload. Once the desired data is obtained, the payload encodes the data as a series of 32 characters (0-9, A-Z) broken into short strings (3KJ242AIE9, P028X977W,…).4. The payload initiates thousands of unique DNS record requests to the attacker’s domain with each string as
The attacker incorporates one of many open-source DNS tunneling kits into an authoritative DNSnameserver (NS) and malicious payload.2. An IP address (e.g. 1.2.3.4) is allocated from the attacker’s infrastructure and a domain name (e.g. attackerdomain.com) is registered or reused. The registrar informs the top-level domain (.com) nameservers to refer requests for attackerdomain.com to ns.attackerdomain.com, which has a DNS record mapped to 1.2.3.43. The attacker compromises a system with the malicious payload. Once the desired data is obtained, the payload encodes the data as a series of 32 characters (0-9, A-Z) broken into short strings (3KJ242AIE9, P028X977W,…).4. The payload initiates thousands of unique DNS record requests to the attacker’s domain with each string as
Reference: https://learn-umbrella.cisco.com/i/775902-dns-tunneling/0
NEW QUESTION 8
Which cloud service offering allows customers to access a web application that is being hosted, managed, and maintained by a cloud service provider?
- A. IaC
- B. SaaS
- C. IaaS
- D. PaaS
Answer: B
NEW QUESTION 9
How is Cisco Umbrella configured to log only security events?
- A. per policy
- B. in the Reporting settings
- C. in the Security Settings section
- D. per network in the Deployments section
Answer: A
Explanation:
Reference: https://docs.umbrella.com/deployment-umbrella/docs/log-management
NEW QUESTION 10
Which Cisco security solution provides patch management in the cloud?
- A. Cisco Umbrella
- B. Cisco ISE
- C. Cisco CloudLock
- D. Cisco Tetration
Answer: C
NEW QUESTION 11
Which feature requires a network discovery policy on the Cisco Firepower Next Generation Intrusion Prevention System?
- A. Security Intelligence
- B. Impact Flags
- C. Health Monitoring
- D. URL Filtering
Answer: B
NEW QUESTION 12
Refer to the exhibit.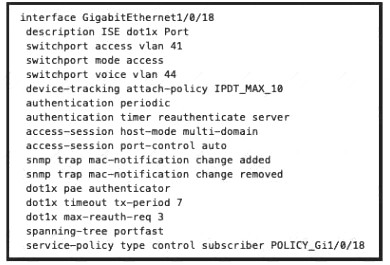
What will occur when this device tries to connect to the port?
- A. 802.1X will not work, but MAB will start and allow the device on the network.
- B. 802.1X will not work and the device will not be allowed network access
- C. 802 1X will work and the device will be allowed on the network
- D. 802 1X and MAB will both be used and ISE can use policy to determine the access level
Answer: B
NEW QUESTION 13
Which attack type attempts to shut down a machine or network so that users are not able to access it?
- A. smurf
- B. bluesnarfing
- C. MAC spoofing
- D. IP spoofing
Answer: A
Explanation:
Denial-of-service (DDoS) aims at shutting down a network or service, causing it to be inaccessible to itsintended users.The Smurf attack is a DDoS attack in which large numbers of Internet Control Message Protocol (ICMP)packets with the intended victim’s spoofed source IP are broadcast to a computer network using an IPbroadcast address.
NEW QUESTION 14
An engineer adds a custom detection policy to a Cisco AMP deployment and encounters issues with the configuration. The simple detection mechanism is configured, but the dashboard indicates that the hash is not 64 characters and is non-zero. What is the issue?
- A. The engineer is attempting to upload a hash created using MD5 instead of SHA-256
- B. The file being uploaded is incompatible with simple detections and must use advanced detections
- C. The hash being uploaded is part of a set in an incorrect format
- D. The engineer is attempting to upload a file instead of a hash
Answer: A
NEW QUESTION 15
Which policy is used to capture host information on the Cisco Firepower Next Generation Intrusion Prevention System?
- A. Correlation
- B. Intrusion
- C. Access Control
- D. Network Discovery
Answer: D
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/security/firepower/640/configuration/guide/fpmc-configguide-v64/introd
NEW QUESTION 16
What is the term for when an endpoint is associated to a provisioning WLAN that is shared with guest access, and the same guest portal is used as the BYOD portal?
- A. single-SSID BYOD
- B. multichannel GUI
- C. dual-SSID BYOD
- D. streamlined access
Answer: C
NEW QUESTION 17
What is a function of Cisco AMP for Endpoints?
- A. It detects DNS attacks
- B. It protects against web-based attacks
- C. It blocks email-based attacks
- D. It automates threat responses of an infected host
Answer: D
NEW QUESTION 18
Refer to the exhibit. When creating an access rule for URL filtering, a network engineer adds certain categories and individual URLs to block. What is the result of the configuration?
- A. Only URLs for botnets with reputation scores of 1-3 will be blocked.
- B. Only URLs for botnets with a reputation score of 3 will be blocked.
- C. Only URLs for botnets with reputation scores of 3-5 will be blocked.
- D. Only URLs for botnets with a reputation score of 3 will be allowed while the rest will be blocked.
Answer: A
NEW QUESTION 19
Which DoS attack uses fragmented packets in an attempt to crash a target machine?
- A. teardrop
- B. smurf
- C. LAND
- D. SYN flood
Answer: A
Explanation:
Reference: https://www.radware.com/security/ddos-knowledge-center/ddospedia/teardrop-attack/
NEW QUESTION 20
......
P.S. Downloadfreepdf.net now are offering 100% pass ensure 350-701 dumps! All 350-701 exam questions have been updated with correct answers: https://www.downloadfreepdf.net/350-701-pdf-download.html (631 New Questions)
