Our pass rate is high to 98.9% and the similarity percentage between our 350-701 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Cisco 350-701 exam in just one try? I am currently studying for the Cisco 350-701 exam. Latest Cisco 350-701 Test exam practice questions and answers, Try Cisco 350-701 Brain Dumps First.
Also have 350-701 free dumps questions for you:
NEW QUESTION 1
Which Cisco ISE feature helps to detect missing patches and helps with remediation?
- A. posture assessment
- B. profiling policy
- C. authentication policy
- D. enabling probes
Answer: B
NEW QUESTION 2
What features does Cisco FTDv provide over ASAv?
- A. Cisco FTDv runs on VMWare while ASAv does not
- B. Cisco FTDv provides 1GB of firewall throughput while Cisco ASAv does not
- C. Cisco FTDv runs on AWS while ASAv does not
- D. Cisco FTDv supports URL filtering while ASAv does not
Answer: D
NEW QUESTION 3
What two mechanisms are used to redirect users to a web portal to authenticate to ISE for guest services? (Choose two)
- A. multiple factor auth
- B. local web auth
- C. single sign-on
- D. central web auth
- E. TACACS+
Answer: BD
NEW QUESTION 4
Drag and drop the common security threats from the left onto the definitions on the right.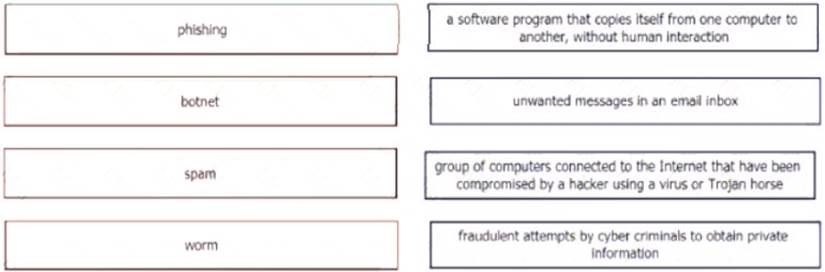
Solution:
A picture containing application Description automatically generated
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 5
Which type of data does the Cisco Stealthwatch system collect and analyze from routers, switches, and firewalls?
- A. NTP
- B. syslog
- C. SNMP
- D. NetFlow
Answer: D
NEW QUESTION 6
For Cisco IOS PKI, which two types of Servers are used as a distribution point for CRLs? (Choose two)
- A. SDP
- B. LDAP
- C. subordinate CA
- D. SCP
- E. HTTP
Answer: BE
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_pki/configuration/15-mt/sec-pki-15-mtbook/sec-pk
NEW QUESTION 7
Which statement about the configuration of Cisco ASA NetFlow v9 Secure Event Logging is true?
- A. To view bandwidth usage for NetFlow records, the QoS feature must be enabled.
- B. A sysopt command can be used to enable NSEL on a specific interface.
- C. NSEL can be used without a collector configured.
- D. A flow-export event type must be defined under a policy
Answer: D
NEW QUESTION 8
An administrator configures a new destination list in Cisco Umbrella so that the organization can block specific domains for its devices. What should be done to ensure that all subdomains of domain.com are blocked?
- A. Configure the *.com address in the block list.
- B. Configure the *.domain.com address in the block list
- C. Configure the *.domain.com address in the block list
- D. Configure the domain.com address in the block list
Answer: C
NEW QUESTION 9
Which two capabilities does an MDM provide? (Choose two.)
- A. delivery of network malware reports to an inbox in a schedule
- B. unified management of mobile devices, Macs, and PCs from a centralized dashboard
- C. enforcement of device security policies from a centralized dashboard
- D. manual identification and classification of client devices
- E. unified management of Android and Apple devices from a centralized dashboard
Answer: BC
NEW QUESTION 10
An engineer must configure Cisco AMP for Endpoints so that it contains a list of files that should not be executed by users. These files must not be quarantined. Which action meets this configuration requirement?
- A. Identity the network IPs and place them in a blocked list.
- B. Modify the advanced custom detection list to include these files.
- C. Create an application control blocked applications list.
- D. Add a list for simple custom detection.
Answer: C
NEW QUESTION 11
Which category includes DoS Attacks?
- A. Virus attacks
- B. Trojan attacks
- C. Flood attacks
- D. Phishing attacks
Answer: C
NEW QUESTION 12
Which functions of an SDN architecture require southbound APIs to enable communication?
- A. SDN controller and the network elements
- B. management console and the SDN controller
- C. management console and the cloud
- D. SDN controller and the cloud
Answer: A
Explanation:
The Southbound API is used to communicate between Controllers and network devices
NEW QUESTION 13
What is the function of the Context Directory Agent?
- A. maintains users’ group memberships
- B. relays user authentication requests from Web Security Appliance to Active Directory
- C. reads the Active Directory logs to map IP addresses to usernames
- D. accepts user authentication requests on behalf of Web Security Appliance for user identification
Answer: C
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/ibf/cda_10/Install_Config_guide/cda10/cda_oveviw.html
NEW QUESTION 14
Which two protocols must be configured to authenticate end users to the Web Security Appliance? (Choose two.)
- A. NTLMSSP
- B. Kerberos
- C. CHAP
- D. TACACS+
- E. RADIUS
Answer: AB
NEW QUESTION 15
Which security solution protects users leveraging DNS-layer security?
- A. Cisco ISE
- B. Cisco FTD
- C. Cisco Umbrella
- D. Cisco ASA
Answer: C
NEW QUESTION 16
What is the purpose of the My Devices Portal in a Cisco ISE environment?
- A. to register new laptops and mobile devices
- B. to request a newly provisioned mobile device
- C. to provision userless and agentless systems
- D. to manage and deploy antivirus definitions and patches on systems owned by the end user
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/ise/2-4/mydevices/b_mydevices_2x.html
NEW QUESTION 17
An engineer enabled SSL decryption for Cisco Umbrella intelligent proxy and needs to ensure that traffic is inspected without alerting end-users.
- A. Upload the organization root CA to the Umbrella admin portal
- B. Modify the user's browser settings to suppress errors from Umbrella.
- C. Restrict access to only websites with trusted third-party signed certificates.
- D. Import the Umbrella root CA into the trusted root store on the user's device.
Answer: A
NEW QUESTION 18
Which feature within Cisco ISE verifies the compliance of an endpoint before providing access to the network?
- A. Posture
- B. Profiling
- C. pxGrid
- D. MAB
Answer: A
NEW QUESTION 19
Which two services must remain as on-premises equipment when a hybrid email solution is deployed? (Choose two)
- A. DDoS
- B. antispam
- C. antivirus
- D. encryption
- E. DLP
Answer: DE
Explanation:
Reference: https://www.cisco.com/c/dam/en/us/td/docs/security/ces/overview_guide/Cisco_Cloud_Hybrid_Email_Security
NEW QUESTION 20
......
Recommend!! Get the Full 350-701 dumps in VCE and PDF From Downloadfreepdf.net, Welcome to Download: https://www.downloadfreepdf.net/350-701-pdf-download.html (New 631 Q&As Version)
