It is impossible to pass Microsoft az-500 exam without any help in the short term. Come to Examcollection soon and find the most advanced, correct and guaranteed Microsoft az-500 practice questions. You will get a surprising result by our Renewal Microsoft Azure Security Technologies practice guides.
Free demo questions for Microsoft az-500 Exam Dumps Below:
NEW QUESTION 1
You have the Azure Information Protection conditions shown in the following table.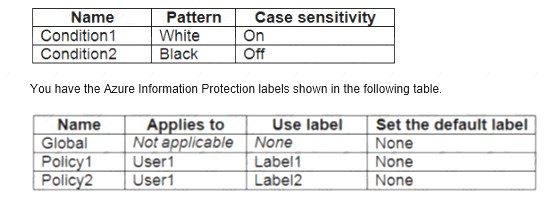
You need to identify how Azure Information Protection will label files.
What should you identify? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.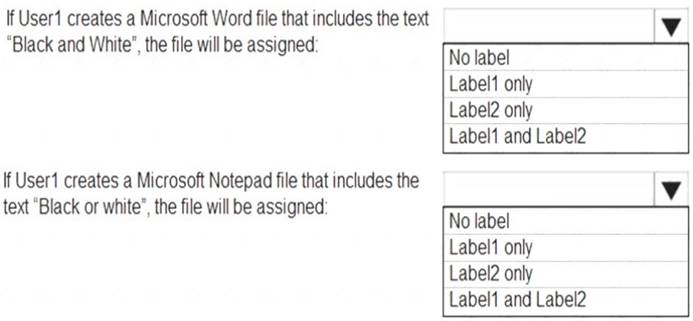
Solution:
Box 1: Label 2 only
How multiple conditions are evaluated when they apply to more than one label
 The labels are ordered for evaluation, according to their position that you specify in the policy: The label positioned first has the lowest position (least sensitive) and the label positioned last has the highest position (most sensitive).
The labels are ordered for evaluation, according to their position that you specify in the policy: The label positioned first has the lowest position (least sensitive) and the label positioned last has the highest position (most sensitive). The most sensitive label is applied.
The most sensitive label is applied.  The last sublabel is applied.
The last sublabel is applied.Box 2: No Label
Automatic classification applies to Word, Excel, and PowerPoint when documents are saved, and apply to Outlook when emails are sent. Automatic classification does not apply to Microsoft Notepad.
References:
https://docs.microsoft.com/en-us/azure/information-protection/configure-policy-classification
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 2
Your company plans to create separate subscriptions for each department. Each subscription will be associated to the same Azure Active Directory (Azure AD) tenant.
You need to configure each subscription to have the same role assignments. What should you use?
- A. Azure Security Center
- B. Azure Blueprints
- C. Azure AD Privileged Identity Management (PIM)
- D. Azure Policy
Answer: B
Explanation:
https://docs.microsoft.com/en-us/azure/governance/blueprints/overview#blueprint-definition https://docs.microsoft.com/en-us/azure/governance/blueprints/overview
NEW QUESTION 3
You plan to use Azure Log Analytics to collect logs from 200 servers that run Windows Server 2016.
You need to automate the deployment of the Microsoft Monitoring Agent to all the servers by using an Azure Resource Manager template.
How should you complete the template? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.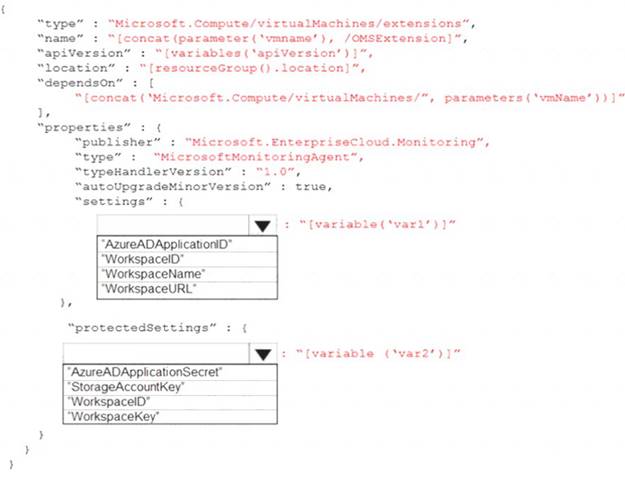
Solution:
References:
https://blogs.technet.microsoft.com/manageabilityguys/2015/11/19/enabling-the-microsoft-monitoring-agent-in
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 4
You have an Azure subscription that contains the resources shown in the following table.
You need to ensure that ServerAdmins can perform the following tasks:  Create virtual machines in RG1 only.
Create virtual machines in RG1 only. Connect the virtual machines to the existing virtual networks in RG2 only.
Connect the virtual machines to the existing virtual networks in RG2 only.
The solution must use the principle of least privilege.
Which two role-based access control (RBAC) roles should you assign to ServerAdmins? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- A. a custom RBAC role for RG2
- B. the Network Contributor role for RG2
- C. the Contributor role for the subscription
- D. a custom RBAC role for the subscription
- E. the Network Contributor role for RG1
- F. the Virtual Machine Contributor role for RG1
Answer: AF
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/role-based-access-control/built-in-roles
NEW QUESTION 5
You have an Azure subscription that uses Azure AD Privileged Identity Management (PIM). A user named User1 is eligible for the Billing administrator role.
You need to ensure that the role can only be used for a maximum of two hours. What should you do?
- A. Create a new access review.
- B. Edit the role assignment settings.
- C. Update the end date of the user assignment
- D. Edit the role activation settings.
Answer: B
NEW QUESTION 6
You have an Azure Active Directory (Azure AD) tenant.
You need to prevent nonprivileged Azure AD users from creating service principals in Azure AD. What should you do in the Azure Active Directory admin center of the tenant?
- A. From the Properties Wade, set Enable Security defaults to Yes.
- B. From the Properties blade, set Access management fen Azure resources to No
- C. From the User settings blade, set Users can register applications to No
- D. From the User settings blade, set Restrict access to Azure AD administration portal to Yes.
Answer: C
NEW QUESTION 7
Your company has an Azure subscription named Subscription1. Subscription1 is associated with the Azure Active Directory tenant that includes the users shown in the following table.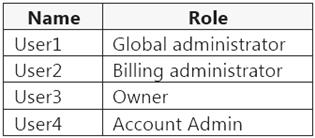
The company is sold to a new owner.
The company needs to transfer ownership of Subscription1.
Which user can transfer the ownership and which tool should the user use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.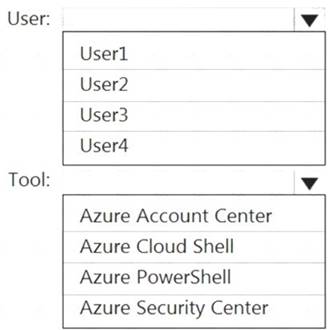
Solution:
Table Description automatically generated
Reference:
https://docs.microsoft.com/en-us/azure/cost-management-billing/manage/billing-subscription-transfer
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 8
You have an Azure SQL Database server named SQL1.
You plan to turn on Advanced Threat Protection for SQL1 to detect all threat detection types. Which action will Advanced Threat Protection detect as a threat?
- A. A user updates more than 50 percent of the records in a table.
- B. A user attempts to sign as SELECT * from table1.
- C. A user is added to the db_owner database role.
- D. A user deletes more than 100 records from the same table.
Answer: B
Explanation:
Advanced Threat Protection can detect potential SQL injections: This alert is triggered when an active exploit happens against an identified application vulnerability to SQL injection. This means the attacker is trying to inject malicious SQL statements using the vulnerable application code or stored procedures.
References:
https://docs.microsoft.com/en-us/azure/sql-database/sql-database-threat-detection-overview
NEW QUESTION 9
You have an Azure Sentinel workspace that has an Azure Active Directory (Azure AD) data connector. You are threat hunting suspicious traffic from a specific IP address.
You need to annotate an intermediate event stored in the workspace and be able to reference the IP address when navigating through the investigation graph.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.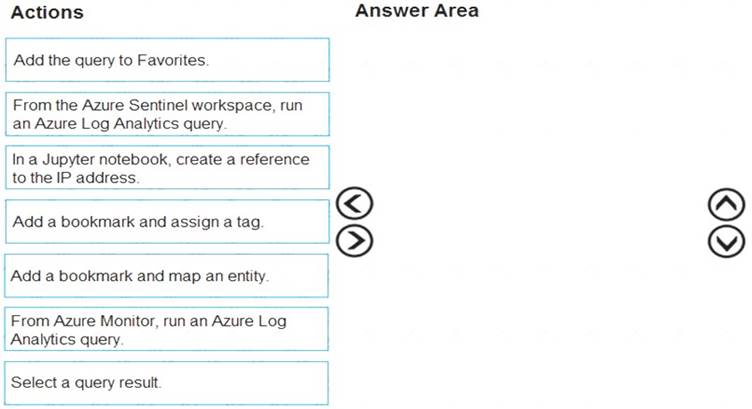
Solution:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/bookmarks
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 10
You have an Azure subscription named Sub1 that contains the Azure key vaults shown in the following table.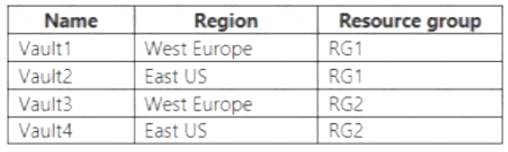
In Sub1, you create a virtual machine that has the following configurations:
• Name:VM1
• Size: DS2v2
• Resource group: RG1
• Region: West Europe
• Operating system: Windows Server 2016
You plan to enable Azure Disk Encryption on VM1.
In which key vaults can you store the encryption key for VM1?
- A. Vault1 or Vault3 only
- B. Vault1, Vault2, Vault3, or Vault4
- C. Vault1 only
- D. Vault1 or Vault2 only
Answer: C
Explanation:
"Your key vault and VMs must be in the same subscription. Also, to ensure that encryption secrets don't cross regional boundaries, Azure Disk Encryption requires the Key Vault and the VMs to be co-located in the same region." https://docs.microsoft.com/en-us/azure/virtual-machines/windows/disk-encryption-key-vault
NEW QUESTION 11
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.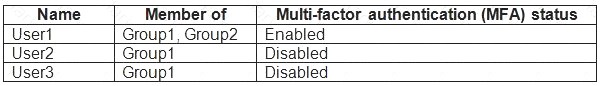
You create and enforce an Azure AD Identity Protection sign-in risk policy that has the following settings:  Assignments: Include Group1, exclude Group2
Assignments: Include Group1, exclude Group2 Conditions: Sign-in risk level: Medium and above
Conditions: Sign-in risk level: Medium and above Access Allow access, Require multi-factor authentication
Access Allow access, Require multi-factor authentication
You need to identify what occurs when the users sign in to Azure AD.
What should you identify for each user? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.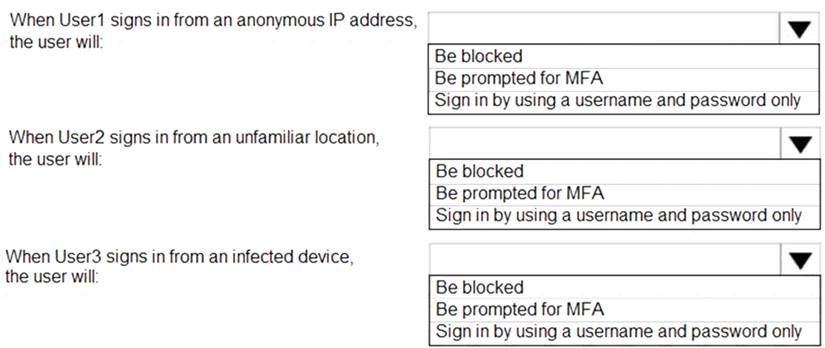
Solution:
References:
http://www.rebeladmin.com/2018/09/step-step-guide-configure-risk-based-azure-conditional-access-policies/ https://docs.microsoft.com/en-us/azure/active-directory/identity-protection/concept-identity-protection-policies https://docs.microsoft.com/en-us/azure/active-directory/identity-protection/concept-identity-protection-risks
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 12
You have an Azure subscription that contains a user named User1. User1 is assigned the Reader role for the subscription.
You plan to create a custom role named Role1 and assign Role1 to User1.
You need to ensure that User1 can create and manage application security groups by using the Azure portal. Which two permissions should you add to Role1? To answer, select the appropriate permission in the answer area.
NOTE: Each correct selection is worth one point.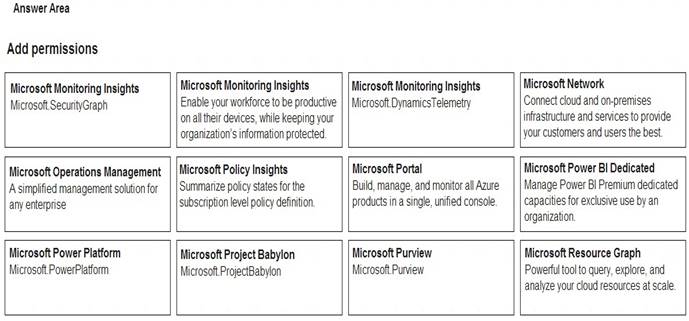
Solution:
* 1. Microsoft Portal 2. Microsoft Network
https://learn.microsoft.com/en-us/azure/azure-resource-manager/management/azure-services-resource-providers
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 13
You have an Azure subscription named Subcription1 that contains the resources shown in the following table.
You have an Azure subscription named Subcription2 that contains the following resources:  An Azure Sentinel workspace
An Azure Sentinel workspace An Azure Event Grid instance
An Azure Event Grid instance
You need to ingest the CEF messages from the NVAs to Azure Sentinel. NOTE: Each correct selection is worth one point.
Solution:

Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 14
You have multiple development teams that will create apps in Azure.
You plan to create a standard development environment that will be deployed for each team.
You need to recommend a solution that will enforce resource locks across the development environments and ensure that the locks are applied in a consistent manner.
What should you include in the recommendation?
- A. an Azure policy
- B. an Azure Resource Manager template
- C. a management group
- D. an Azure blueprint
Answer: D
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/governance/blueprints/concepts/resource-locking
NEW QUESTION 15
You have an Azure subscription that contains the resources shown in the following table.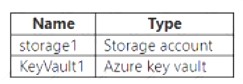
You need to configure storage1 to regenerate keys automatically every 90 days. Which cmdlet should you run?
- A. set -A=StorageAccount
- B. Add-A:StorogcAccountmanagementPolicyAction
- C. Set-A;StorageAccountimanagementPolicy
- D. Add-AsKeyVaultmanageStorageAccount
Answer: D
NEW QUESTION 16
You have an Azure subscription that contains an Azure Active Directory (Azure AD) tenant named contoso.com. The tenant contains the users shown in the following table.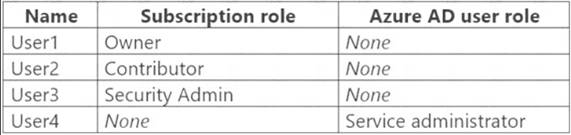
You create a resource group named RG1.
Which users can modify the permissions for RG1 and which users can create virtual networks in RG1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.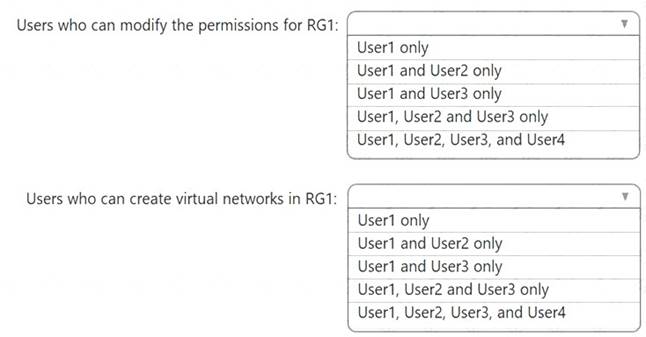
Solution:
Box 1: Only an owner can change permissions on resources.
Box 2: A Contributor can create/modify/delete anything in the subscription but cannot change permissions.
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 17
You have an Azure subscription.
You plan to create a workflow automation in Azure Security Center that will automatically remediate a security vulnerability.
What should you create first?
- A. a managed identity
- B. an automation account
- C. an Azure function app
- D. an alert rule
- E. an Azure logic app
Answer: E
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/security-center/workflow-automation
NEW QUESTION 18
DRAG DROP
You create an Azure subscription.
You need to ensure that you can use Azure Active Directory (Azure AD) Privileged Identity Management (PIM) to secure Azure AD roles.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.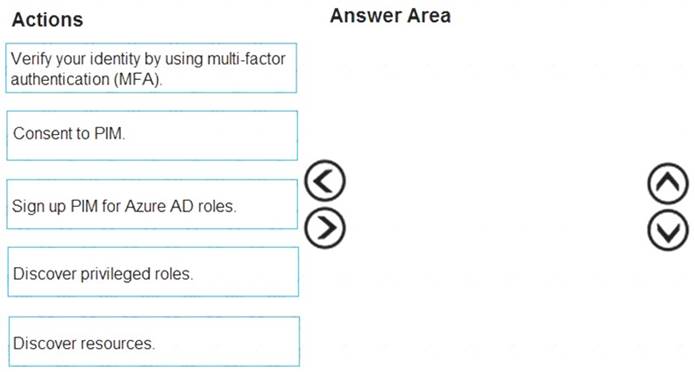
Solution:
Step 1: Consent to PIM
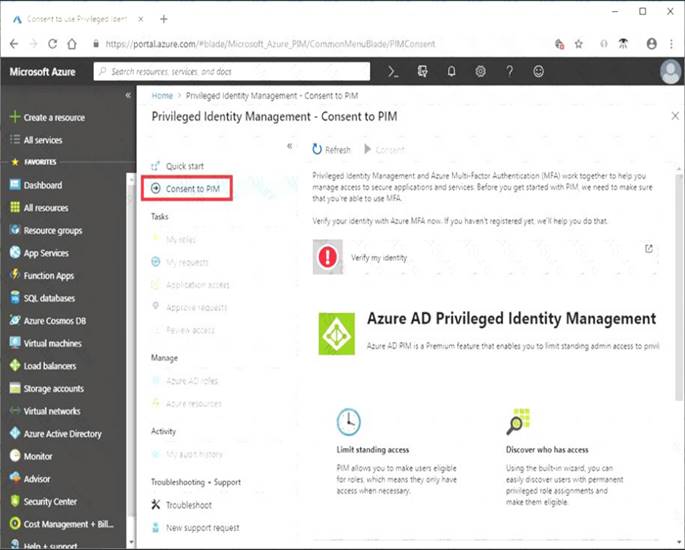
Step: 2 Verify your identity by using multi-factor authentication (MFA)
Click Verify my identity to verify your identity with Azure MFA. You'll be asked to pick an account. Step 3: Sign up PIM for Azure AD roles
Once you have enabled PIM for your directory, you'll need to sign up PIM to manage Azure AD roles. References:
https://docs.microsoft.com/en-us/azure/active-directory/privileged-identity-management/pim-getting-started
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 19
......
Thanks for reading the newest az-500 exam dumps! We recommend you to try the PREMIUM Thedumpscentre.com az-500 dumps in VCE and PDF here: https://www.thedumpscentre.com/az-500-dumps/ (416 Q&As Dumps)
