Examcollection az-500 Questions are updated and all az-500 answers are verified by experts. Once you have completely prepared with our az-500 exam prep kits you will be ready for the real az-500 exam without a problem. We have Improve Microsoft az-500 dumps study guide. PASSED az-500 First attempt! Here What I Did.
Microsoft az-500 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
You have an Azure subscription that contains the virtual machines shown in the following table.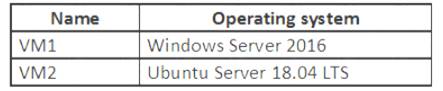
From Azure Security Center, you turn on Auto Provisioning. You deploy the virtual machines shown in the following table.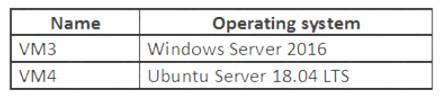
On which virtual machines is the Log Analytics agent installed?
- A. VM3 only
- B. VM1 and VM3 only
- C. VM3 and VM4 only
- D. VM1, VM2, VM3, and VM4
Answer: D
Explanation:
When automatic provisioning is On, Security Center provisions the Log Analytics Agent on all supported Azure VMs and any new ones that are created.
Supported Operating systems include: Ubuntu 14.04 LTS (x86/x64), 16.04 LTS (x86/x64), and 18.04 LTS (x64) and Windows Server 2008 R2, 2012, 2012 R2, 2016, version 1709 and 1803
Reference:
https://docs.microsoft.com/en-us/azure/security-center/security-center-enable-data-collection
NEW QUESTION 2
You have the Azure resource shown in the following table.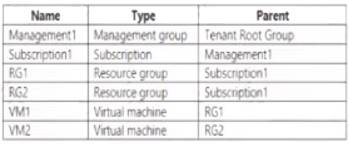
You need to meet the following requirements:
* Internet-facing virtual machines must be protected by using network security groups (NSGs).
* All the virtual machines must have disk encryption enabled.
What is the minimum number of security that you should create in Azure Security Center?
- A. 1
- B. 2
- C. 3
- D. 4
Answer: D
NEW QUESTION 3
You have an Azure subscription that contains three storage accounts, an Azure SQL managed instance named SQL and three Azure SQL databases. The storage accounts are configured as shown in the following table.
SQ11 has the following settings:
• Auditing: On
• Audit tog destination: storage1
The Azure SQL databases are configured as shown in the following table.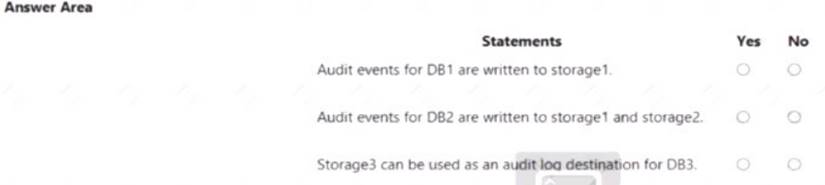
Solution:
Reference:
https://docs.microsoft.com/en-us/azure/azure-sql/managed-instance/auditing-configure https://docs.microsoft.com/en-us/azure/azure-sql/database/auditing-overview
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 4
You have an Azure subscription that contains an Azure SQL database named SQLDB1. SQLDB1 contains the columns shown in the following table.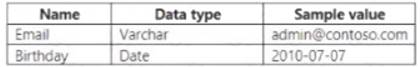
For the Email and Birthday columns, you implement dynamic data masking by using the default masking function.
Which value will the users see in each column? To answer, drag the appropriate values to the correct columns. Each value may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Solution:

Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 5
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have an Azure Subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sa1 by using several shared access signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service. You need to revoke all access to Sa1.
Solution: You create a new stored access policy. Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
Shared access signatures provides access to a particular resource such as blog. Stored access policies are a group of Shared Access Signatures (SAS). In order to revoke access to a SAS you can either:
* 1. Rotate the Key1 or Key 2, that is the access keys used to sign the SAS. Rotating the access keys used to sign the SAS, invalidates any previously signed SAS hence revoking the SAS issused before
* 2. Remove the stored access policy which an SAS is linked to. If a Stored Access Policy is removed, it also invalidates the SASs liked to the Stored Access Policy.
NEW QUESTION 6
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have an Amazon Web Services (AWS) account.
You need to ensure that when you deploy a new AWS Elastic Compute Cloud (EC2) instance, the Microsoft Defender for Servers agent installs automatically.
What should you configure first?
- A. the log Analytics agent
- B. the Azure Monitor agent
- C. the native cloud connector
- D. the classic cloud connector
Answer: A
NEW QUESTION 7
You plan to deploy an app that will modify the properties of Azure Active Directory (Azure AD) users by using Microsoft Graph. You need to ensure that the app can access Azure AD. What should you configure first?
- A. a custom role-based access control (RBAC) role
- B. an external identity
- C. an Azure AD Application Proxy
- D. an app registration
Answer: D
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-how-applications-are-added
NEW QUESTION 8
You have an Azure subscription that contains a resource group named RG1. RG1 contains a virtual machine named VM1 that uses Azure Active Directory (Azure AD) authentication.
You have two custom Azure roles named Role1 and Role2 that are scoped to RG1.
The permissions for Role1 are shown in the following JSON code.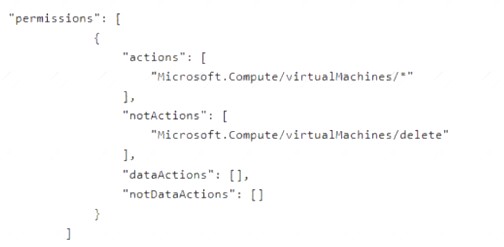
The permissions for Role2 are shown in the following JSON code.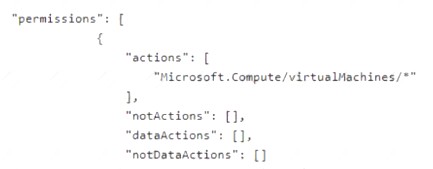
You assign the roles to the users shown in the following table.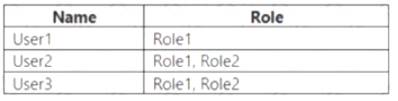
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.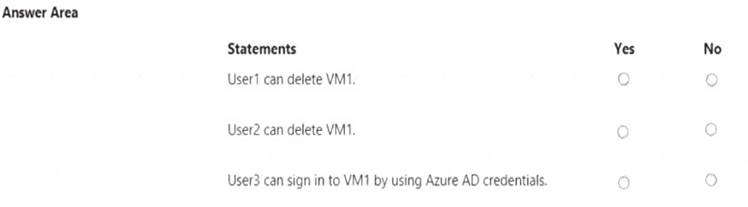
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 9
You have an Azure subscription that contains an Azure Active Directory (Azure AD) tenant and a user named User1.
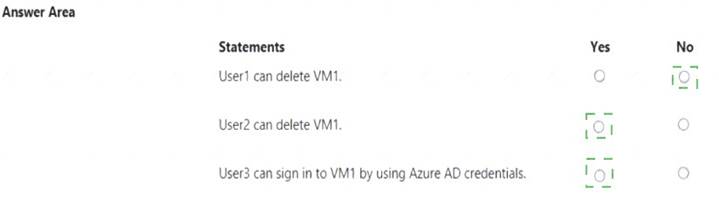
The App registrations settings for the tenant are configured as shown in the following exhibit.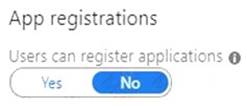
You plan to deploy an app named App1.
You need to ensure that User1 can register App1 in Azure AD. The solution must use the principle of least privilege.
Which role should you assign to User1?
- A. App Configuration Data Owner for the subscription
- B. Managed Application Contributor for the subscription
- C. Cloud application administrator in Azure AD
- D. Application developer in Azure AD.
Answer: D
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/roles/delegate-by-task
NEW QUESTION 10
You have an Azure key vault.
You need to delegate administrative access to the key vault to meet the following requirements: Provide a user named User1 with the ability to set advanced access policies for the key vault.
Provide a user named User1 with the ability to set advanced access policies for the key vault.  Provide a user named User2 with the ability to add and delete certificates in the key vault.
Provide a user named User2 with the ability to add and delete certificates in the key vault. Use the principle of least privilege.
Use the principle of least privilege.
What should you use to assign access to each user? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Solution:
User1: RBAC
RBAC is used as the Key Vault access control mechanism for the management plane. It would allow a user with the proper identity to:
 set Key Vault access policies
set Key Vault access policies create, read, update, and delete key vaults
create, read, update, and delete key vaults  set Key Vault tags
set Key Vault tagsNote: Role-based access control (RBAC) is a system that provides fine-grained access management of Azure resources. Using RBAC, you can segregate duties within your team and grant only the amount of access to users that they need to perform their jobs.
User2: A key vault access policy
A key vault access policy is the access control mechanism to get access to the key vault data plane. Key Vault access policies grant permissions separately to keys, secrets, and certificates.
References:
https://docs.microsoft.com/en-us/azure/key-vault/key-vault-secure-your-key-vault
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 11
You are testing an Azure Kubernetes Service (AKS) cluster. The cluster is configured as shown in the exhibit. (Click the Exhibit tab.)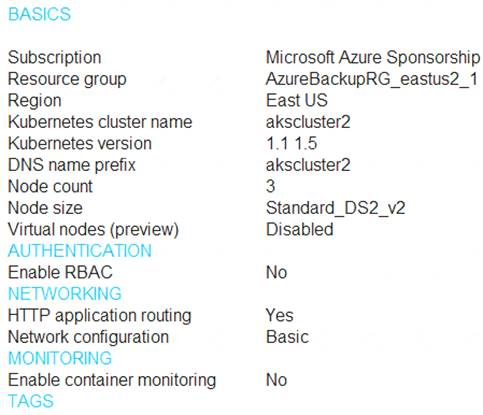
You plan to deploy the cluster to production. You disable HTTP application routing.
You need to implement application routing that will provide reverse proxy and TLS termination for AKS services by using a single IP address.
What should you do?
- A. Create an AKS Ingress controller.
- B. Install the container network interface (CNI) plug-in.
- C. Create an Azure Standard Load Balancer.
- D. Create an Azure Basic Load Balancer.
Answer: A
Explanation:
An ingress controller is a piece of software that provides reverse proxy, configurable traffic routing, and TLS termination for Kubernetes services.
References:
https://docs.microsoft.com/en-us/azure/aks/ingress-tls
NEW QUESTION 12
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have an Amazon Web Service (AWS) account named AWS1 that is connected to defender for Cloud.
You need to ensure that AWS foundational Security Best Practices. The solution must minimize administrate effort.
What should do you in Defender for Cloud?
- A. Create a new customer assessment.
- B. Assign a built-in assessment.
- C. Assign a built-in compliance standard.
- D. Create a new custom standard.
Answer: C
NEW QUESTION 13
You have an Azure Active Directory (Azure AD) tenant named contoso1812.onmicrosoft.com that contains the users shown in the following table.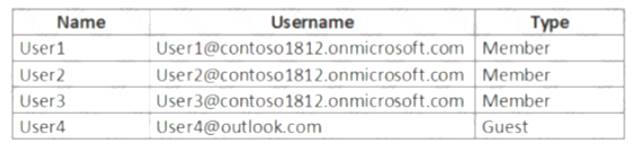
You create an Azure Information Protection label named Label1. The Protection settings for Label1 are configured as shown in the exhibit. (Click the Exhibit tab.)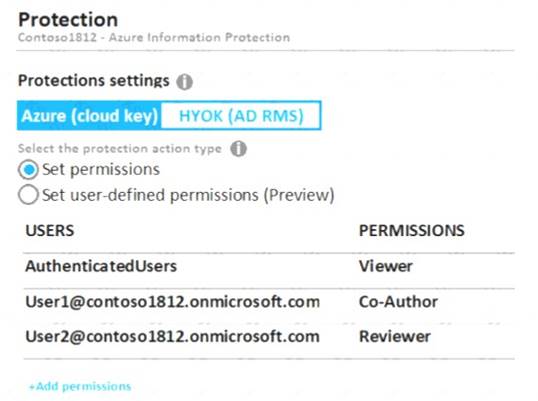
Label1 is applied to a file named File1.
For each of the following statements, select Yes if the statement is true, Otherwise, select No. NOTE: Each correct selection is worth one point.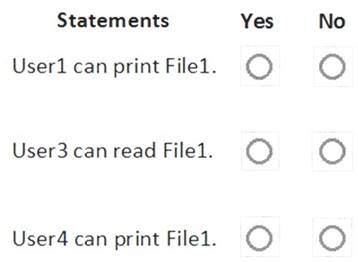
Solution:
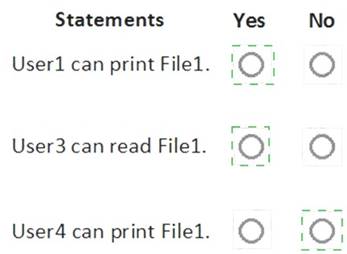
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 14
You have an Azure subscription that contains a user named User1 and an Azure Container Registry named ConReg1.
You enable content trust for ContReg1.
You need to ensure that User1 can create trusted images in ContReg1. The solution must use the principle of least privilege.
Which two roles should you assign to User1? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A. AcrQuarantineReader
- B. Contributor
- C. AcrPush
- D. AcrImageSigner
- E. AcrQuarantineWriter
Answer: CD
Explanation:
References:
https://docs.microsoft.com/en-us/azure/container-registry/container-registry-content-trust https://docs.microsoft.com/en-us/azure/container-registry/container-registry-roles
NEW QUESTION 15
Lab Task
use the following login credentials as needed:
To enter your username, place your cursor in the Sign in box and click on the username below.
To enter your password. place your cursor in the Enter password box and click on the password below. Azure Username: Userl -28681041@ExamUsers.com
Azure Password: GpOAe4@lDg
If the Azure portal does not load successfully in the browser, press CTRL-K to reload the portal in a new browser tab.
The following information is for technical support purposes only: Lab Instance: 28681041
Task 3
The developers at your company plan to create a web app named App28681041 and to publish the app to https://www.contoso.com. You need to perform the following tasks:
• Ensure that App28681041 is registered to Azure AD.
• Generate a password for App28681041.
Solution:
To register App28681041 to Azure AD and generate a password for it, you can follow these steps:
 In the Azure portal, search for and select Azure Active Directory.
In the Azure portal, search for and select Azure Active Directory.  In the left pane, select App registrations.
In the left pane, select App registrations. Select New registration.
Select New registration. In the Register an application pane, enter the following information:
In the Register an application pane, enter the following information:  Name: App28681041
Name: App28681041 Supported account types: Select the appropriate account types for your scenario.
Supported account types: Select the appropriate account types for your scenario.  Redirect URI: Leave this field blank.
Redirect URI: Leave this field blank. Select Register.
Select Register. In the App registrations pane, select the newly created App28681041 application.
In the App registrations pane, select the newly created App28681041 application.  In the left pane, select Certificates & secrets.
In the left pane, select Certificates & secrets. Select New client secret.
Select New client secret. In the Add a client secret pane, enter the following information:
In the Add a client secret pane, enter the following information:  Description: Enter a description for the client secret.
Description: Enter a description for the client secret. Expires: Select an appropriate expiration date for the client secret.
Expires: Select an appropriate expiration date for the client secret. Select Add.
Select Add. In the Certificates & secrets pane, copy the value of the newly created client secret.
In the Certificates & secrets pane, copy the value of the newly created client secret.You can find more information on this topic in the following Microsoft documentation: Quickstart: Register an application with the Microsoft identity platform.
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 16
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions. You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create a resource graph and an assignment that is scoped to a management group. Does this meet the goal?
- A. Yes
- B. No
Answer: B
Explanation:
References:
https://docs.microsoft.com/en-us/azure/governance/management-groups/create
NEW QUESTION 17
You have an Azure subscription that contains a web app named App1.
Users must be able to select between a Google identity or a Microsoft identity when authenticating to App1. You need to add Google as an identity provider in Azure AD.
Which two pieces of information should you configure? Each correct answer presents part of the solution. Each correct selection is worth one point
- A. a tenant name
- B. a tenant ID
- C. the endpoint URL Of an application
- D. a client ID
- E. a client secret
Answer: DE
Explanation:
https://learn.microsoft.com/en-us/azure/app-service/configure-authentication-provider-google
NEW QUESTION 18
You have an Azure subscription that contains four Azure SQL managed instances.
You need to evaluate the vulnerability of the managed instances to SQL injection attacks. What should you do first?
- A. Create an Azure Sentinel workspace.
- B. Enable Advanced Data Security.
- C. Add the SQL Health Check solution to Azure Monitor.
- D. Create an Azure Advanced Threat Protection (ATP) instance.
Answer: B
NEW QUESTION 19
......
Recommend!! Get the Full az-500 dumps in VCE and PDF From Certshared, Welcome to Download: https://www.certshared.com/exam/az-500/ (New 416 Q&As Version)
